Reflection Blog #3 – Cybersecurity
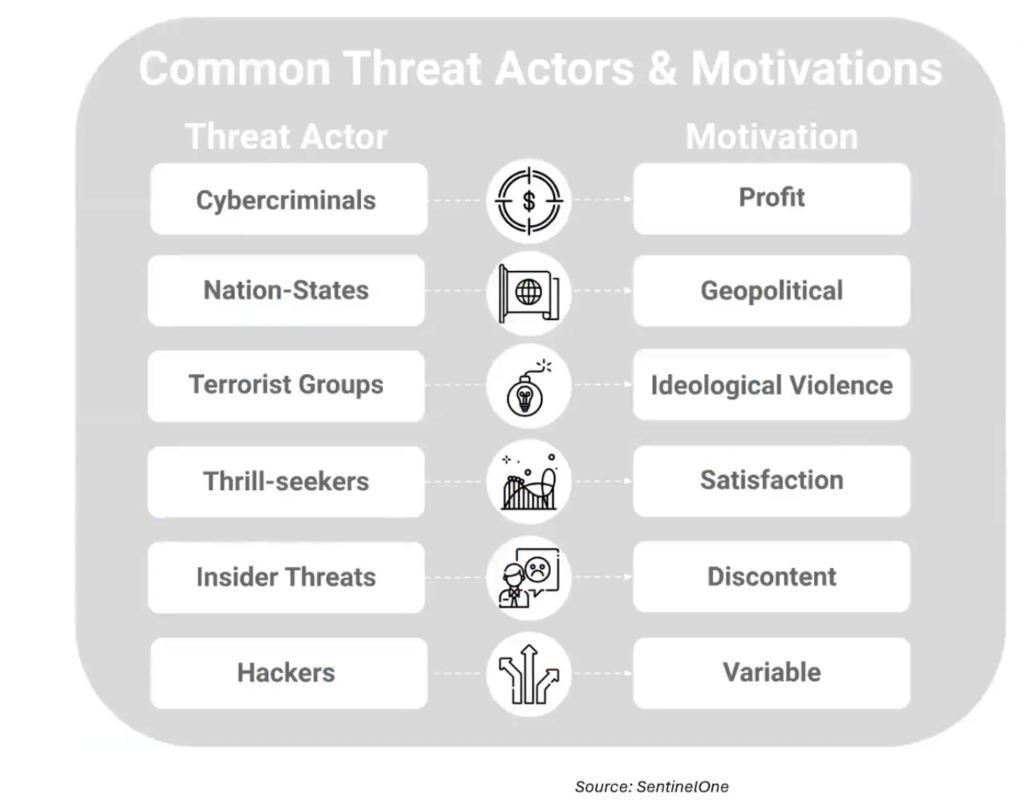
Cybercrime is no longer the domain of the stereotypical “hacker in a hoodie.” It has become a massive, profit-driven industry. To put the scale in perspective, global cybercrime is projected to cost $10.5 trillion USD, making it more profitable than the entire global drug trade combined. Some common threat actors and motives are shown in the picture below:
The AI Double-Edged Sword
Artificial Intelligence (AI) and Machine Learning (ML) have revolutionized both defense and offense. While AI helps defenders identify patterns and block attacks faster, it also lowers the barrier to entry for criminals. Some examples include:
- Hyper-Personalization: Attackers use Large Language Models (LLMs) to write perfect, typo-free phishing emails that mimic a person’s specific writing style.
- Deepfakes: Generative AI can create fake audio or video to impersonate executives or family members in social engineering scams.
- Adversarial AI: This involves poisoning a system by feeding it bad data to confuse or manipulate its decision-making process.
Even Students are Targeted
A common misconception is that individual students aren’t worth a hacker’s time. In reality, students are high-value targets because their credentials provide a foot in the door to larger university systems. Common scams to watch out for include:
- The Piano or Camper Van Scam: Offers free high-value items but asks you to move the conversation to a personal email to evade security monitoring.
- The Student Grant Scam: Impersonates legitimate granting agencies to get you to open malware-infected attachments.
- The Urgent Task Scam: Impersonates a professor or department head asking for a quick favor, often leading to a request for gift cards or office furniture reimbursement.
Best Practices
While the threats are complex, the defences are often simple. High-frequency attacks 90% of which start with phishing can be thwarted with basic digital knowledge. Here are some of the best ways to protect yourself:
- Multi-Factor Authentication (MFA): This is your strongest secondary defence. Never share your MFA codes with anyone.
- Use a VPN (Virtual Private Network): When using public Wi-Fi at a cafe or airport, a VPN encrypts your traffic so it cannot be intercepted by others on the same network.
- Password Managers: Don’t reuse passwords. A password manager allows you to use long, complex, unique strings for every site while only needing to remember one master key.
- Patch Your Systems: When your phone or laptop asks to update, do it. These updates often contain critical security patches for unpatched vulnerabilities that hackers love to exploit.
Final Thoughts
Cybersecurity is deeply integrated with privacy, ethics, and AI. By developing secure and ethical habits now, you aren’t just protecting your current grades or bank account; you are building a professional skillset that is in massive demand. With a global shortage of 3.5 million cybersecurity professionals, staying vigilant is not just a safety measure, it’s a career advantage.